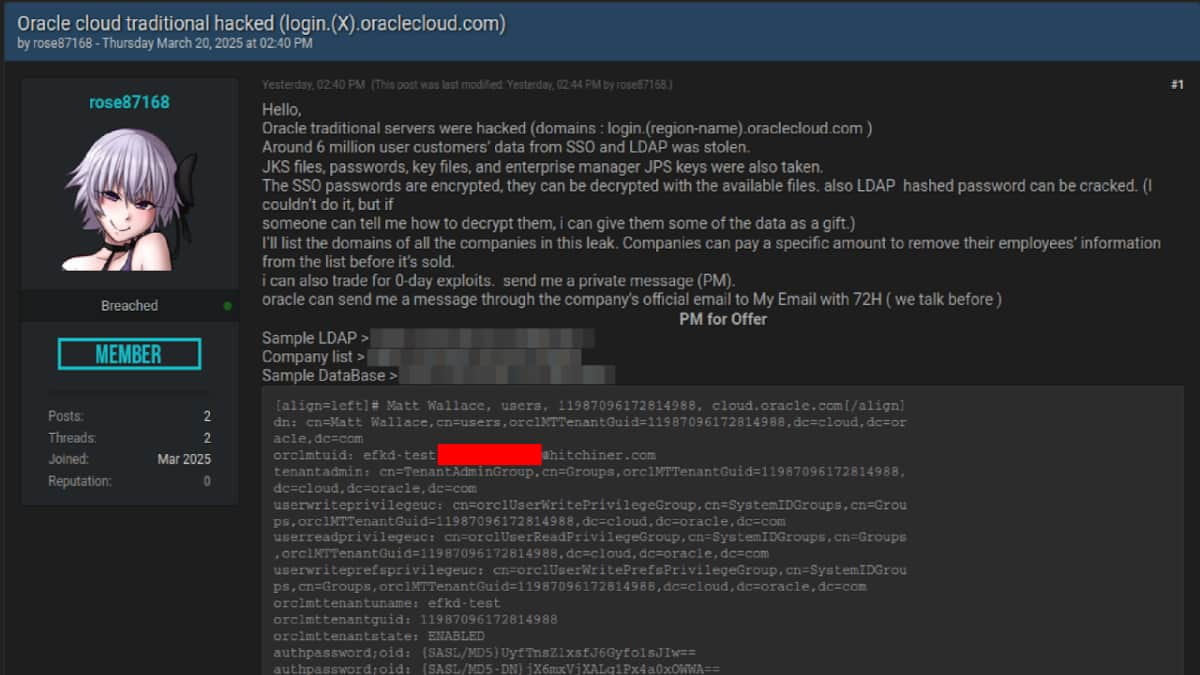
A latest investigation by CloudSEK’s XVigil platform has uncovered a cyberattack focusing on Oracle Cloud, ensuing within the exfiltration of six million information and doubtlessly affecting over 140,000 tenants. Reportedly, a menace actor, recognized as ‘rose87168,’ perpetrated this assault that concerned the theft of delicate knowledge, together with JKS information, encrypted SSO passwords, key information, and enterprise supervisor JPS keys, which are actually being offered on Breach Boards and different darkish internet boards.
The attacker, lively since January 2025, claims to have compromised a subdomain login.us2.oraclecloud.com, which has since been taken down. This subdomain was discovered to be internet hosting Oracle Fusion Middleware 11G, as evidenced by a Wayback Machine seize from February 17, 2025. They’re demanding ransom funds from affected tenants for the removing of their knowledge and have even provided incentives for help in decrypting the stolen SSO and LDAP passwords.
CloudSEK’s evaluation signifies that the menace actor might have compromised a susceptible model of Oracle Cloud servers, doubtlessly leveraging an older flaw, CVE-2021-35587, which impacts Oracle Fusion Middleware (OpenSSO Agent) with the next recognized because the impacted variations:
- 11.1.2.3.0
- 12.2.1.3.0
- 12.2.1.4.0
This CVE, added to the CISA KEV catalogue in December 2022, permits unauthenticated attackers to compromise Oracle Entry Supervisor, doubtlessly main to an entire takeover. This aligns with the kind of knowledge exfiltrated and shared by the attacker. Its exploitation may permit attackers to realize preliminary entry to the atmosphere after which transfer laterally inside the Oracle Cloud atmosphere to entry different methods and knowledge. Additional investigation revealed that the Oracle Fusion Middleware server was final up to date round September 27, 2014, indicating outdated software program.
“Attributable to lack of patch administration practices and/or insecure coding, the vulnerability in Oracle Fusion Middleware was exploited by the menace actor. This simply exploitable vulnerability permits an unauthenticated attacker with community entry by way of HTTP to compromise Oracle Entry Supervisor,” CloudSEK researchers famous within the blog post shared solely with Hackread.com.
Nonetheless, Oracle has issued a statement denying any breach of its cloud infrastructure. “There was no breach of Oracle Cloud. The printed credentials are usually not for the Oracle Cloud. No Oracle Cloud clients skilled a breach or misplaced any knowledge,” Oracle acknowledged in response to the stories. This straight contradicts CloudSEK’s findings and the attacker’s claims.
Nonetheless, if it occurred the breach’s impression could possibly be substantial because the publicity of a whopping six million information raises the danger of unauthorized entry and company espionage. The exfiltration of JKS information is most regarding as these include cryptographic keys, which could possibly be used to decrypt delicate knowledge or achieve entry to different methods inside the affected organizations. Furthermore, the compromise of encrypted SSO and LDAP passwords may result in additional breaches throughout Oracle Cloud environments. The usage of a zero-day vulnerability additionally raises issues concerning the general safety of Oracle Cloud.
CloudSEK recommends fast credential rotation, thorough incident response and forensics, steady menace intelligence monitoring, and engagement with Oracle Safety for verification and mitigation. Additionally they advise strengthening entry controls to stop future incidents.