A brand new phishing marketing campaign has been tricking customers into giving out entry to their Meta Business accounts particularly Instagram. The rip-off, detected by the Cofense Phishing Protection Middle, makes use of faux chat help, detailed directions, and makes an attempt so as to add itself as a safe login methodology to hijack enterprise accounts.
The phishing marketing campaign begins with a faux Instagram alert electronic mail stating that the person’s adverts are suspended attributable to a violation of promoting legal guidelines. The e-mail, which seems to be from Instagram’s help workforce, asks the person to click on on a “Test extra Particulars” button to resolve the difficulty. Nevertheless, the e-mail is definitely despatched from a Salesforce tackle ([email protected]), not Instagram’s official help electronic mail.
This rip-off is loads just like the one which hit Fb customers again in February 2025, the place scammers used automated Salesforce emails to trick individuals into giving up their login credentials by pretending to be Facebook Copyright Notices.
Pretend Chat Assist by way of Chatbot, Phishing and 2FA – All in One Rip-off
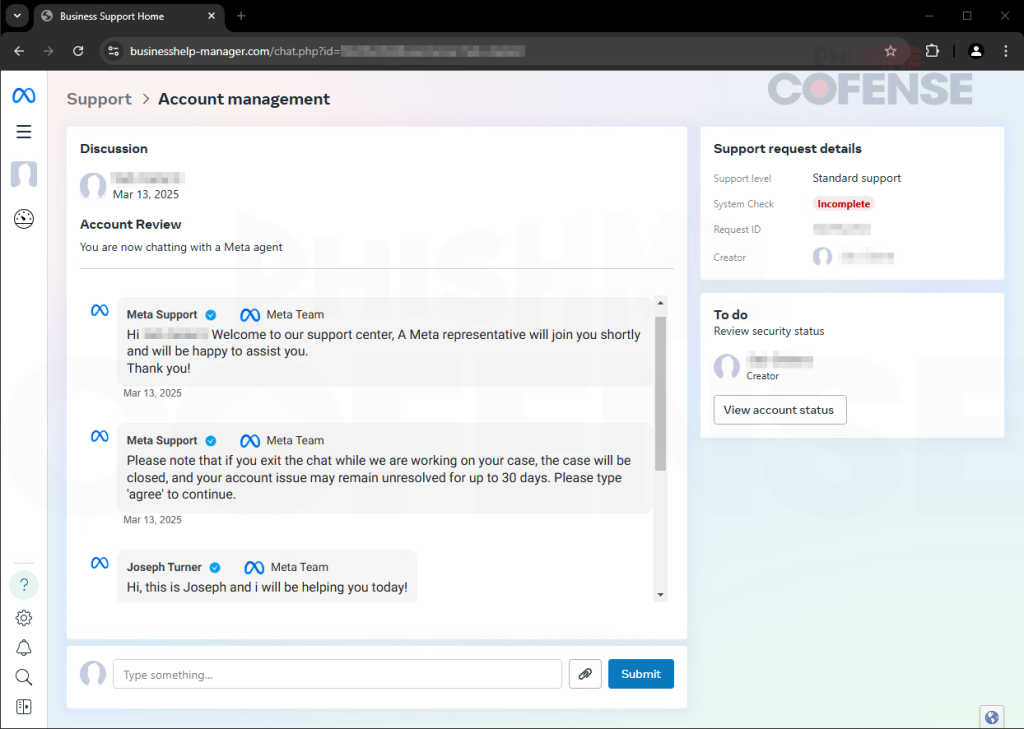
Within the newest rip-off, when the person clicks on the hyperlink for extra particulars, they’re redirected to a faux web page (businesshelp-managercom) that appears much like a professional Meta Enterprise web page. The web page informs the person that their account is vulnerable to suspension and termination and asks them to enter their title and enterprise electronic mail to proceed to a chat help agent.
The attacker then makes use of two strategies to hijack the enterprise account: a faux tech help chatbot or a supposed “setup information” with step-by-step directions. The chatbot asks the person for screenshots of their enterprise account and private data, whereas the setup information offers directions on find out how to add Two-Factor Authentication (2FA) to the person’s enterprise account.
If the chatbot phishing try is unsuccessful, the attacker offers an educational information for including Two-Issue Authentication (2FA) to the person’s enterprise account. This information mimics a do-it-yourself approach to “repair” the person’s account. Customers are directed to click on on a “View Account Standing” button, which reveals detailed directions on find out how to begin a “System Test” and repair the issue themselves. Nevertheless, following these steps provides the attacker one other approach to log in to the Enterprise Meta account by way of the hacker’s Authenticator app named “SYSTEM CHECK.”
In line with Cofence’s blog post shared with Hackread.com, the attackers have put numerous effort into making the rip-off look professional. The emails and touchdown pages intently resemble official Meta communications, and the inclusion of reside agent help provides a layer of deception. The attackers even present video directions detailing find out how to trick the person into including them as a 2FA methodology.
What Customers Ought to Do
This phishing marketing campaign stands out from the standard scams and highlights why everybody who makes use of social media ought to pay attention to frequent social engineering tricks that scammers use nowadays. At all times double-check the sender and take a detailed take a look at the URL earlier than clicking on something. Utilizing apps like Google Authenticator and Microsoft Authenticator may also help block login makes an attempt from suspicious locations and unknown gadgets.