A latest evaluation revealed by Infoblox reveals a classy phishing operation, dubbed Morphing Meerkat, actively exploiting DNS vulnerabilities for years to conduct extremely efficient phishing campaigns.
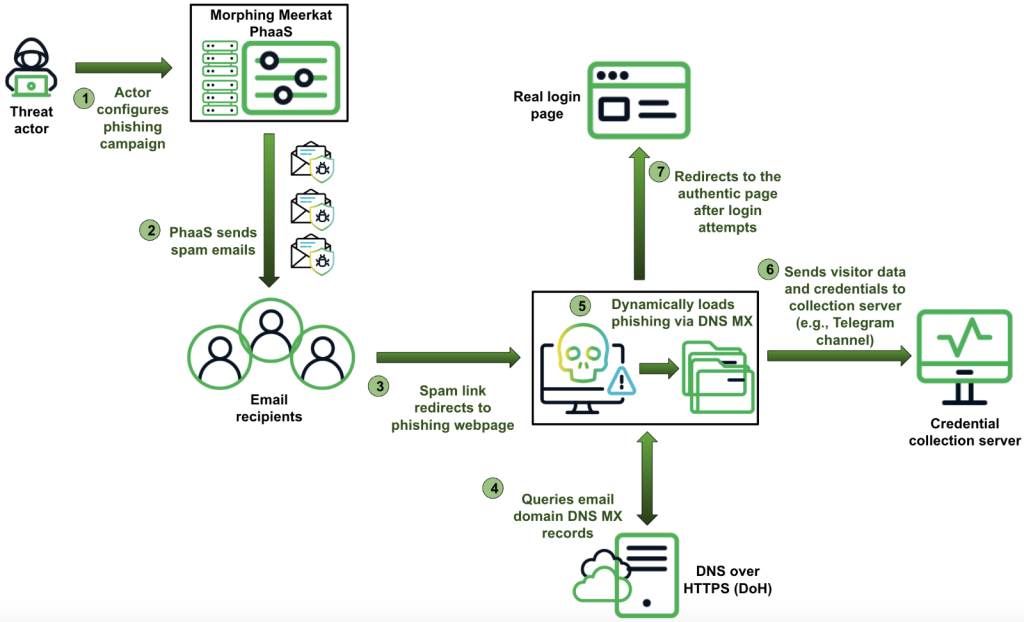
In accordance with researchers, this operation makes use of a phishing-as-a-service (PhaaS) platform, enabling each technical and non-technical cybercriminals to launch focused assaults.
The platform is provided with instruments to bypass safety methods, together with the exploitation of open redirects on adtech servers, redirection by compromised WordPress websites, and using DNS MX information to establish sufferer electronic mail service suppliers. Additionally, they use mass spam supply and dynamic content material tailoring to evade conventional safety measures.
“We’ve got found a phishing equipment that creatively employs DNS mail trade (MX) information to dynamically serve faux, tailor-made, login pages, spoofing over 100 manufacturers,” researchers famous within the blog post, shared with Hackread.com forward of its launch.
Concerning the distribution of spam emails, the platform’s major assault vector, researchers noticed a definite centralization sample, with a substantial portion originating from servers hosted by iomart (United Kingdom) and HostPapa (United States), indicating a unified community moderately than dispersed exercise from a number of impartial entities.
Morphing Meerkat makes use of a dynamic serving of faux login pages personalized to the sufferer’s electronic mail service supplier by querying DNS MX records utilizing Cloudflare DoH or Google Public DNS. The platform maps these information to corresponding phishing HTML information, that includes over 114 distinctive model designs, guaranteeing a personalised phishing expertise and growing the chance of profitable credential theft.
The operation has advanced considerably since its detection in January 2020. Initially, it focused solely 5 electronic mail manufacturers (Gmail, Outlook, AOL, Workplace 365, and Yahoo) and lacked translation capabilities. By July 2023, it had built-in DNS MX records-based dynamic loading of phishing pages and now helps dynamic translation into over a dozen languages, together with English, Korean, Spanish, Russian, German, Chinese language, and Japanese.
To reap stolen credentials, they make the most of a number of strategies, together with electronic mail supply by way of EmailJS, PHP scripts, AJAX requests, and communication with Telegram channels utilizing net API hooks. The platform additionally implements anti-analysis measures, reminiscent of disabling keyboard shortcuts and mouse right-clicks and obfuscating code to hinder safety researchers.
As Infoblox factors out, “reasonably superior web customers and safety researchers usually confirm the malicious state of a phishing webpage by inspecting its HTML code.” Morphing Meerkat counters this by actively blocking such inspection.

Using open redirect vulnerabilities on adtech platforms, notably DoubleClick, permits the risk actors to bypass electronic mail safety methods by leveraging the area’s excessive repute. The platform additionally employs cloaking strategies, redirecting customers to professional login pages and inflating code with non-functional parts, complicating risk evaluation.
Contemplating the platform’s potential to take advantage of safety blind spots by open redirects, DoH communication, and file-sharing companies, it’s important that organizations strengthen DNS safety, limit DoH communication, and restrict entry to non-essential infrastructure to stop exploitation.