A brand new cyberattack marketing campaign found by FortiGuard Labs, Fortinet’s menace intelligence and analysis unit, leverages a mix of social engineering, multi-stage malware, and the manipulation of trusted cloud providers to realize management over compromised methods.
Based on FortiGuard’s investigation, shared with Hackread.com forward of its publishing on Monday, the marketing campaign targets Microsoft Windows users and has a excessive severity degree. Their most important statement is that the attackers have innovated by integrating a modified model of the Havoc framework, Havoc Demon Agent, with the Microsoft Graph API, successfully hiding their malicious communications inside the authentic visitors of well-known cloud providers.
On your data, Havoc is an open-source post-exploitation command and management framework utilized in crimson teaming workout routines and assault campaigns to acquire full management of the goal system.
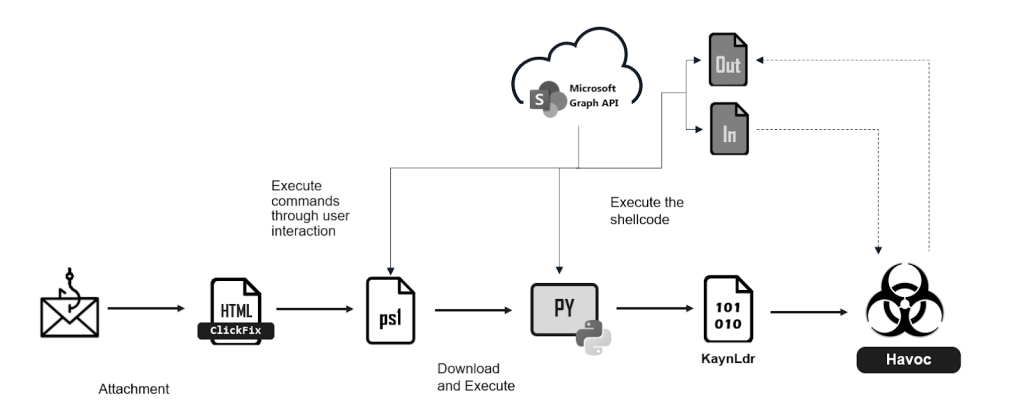
The preliminary level of entry for this assault is a fastidiously crafted phishing e-mail, which accommodates an HTML attachment designed to deceive the recipient into executing a malicious PowerShell command.
By way of a way referred to as “ClickFix,” wherein customers are tricked into executing malicious instructions, the attachment presents a faux error message, prompting the recipient to repeat and paste a seemingly innocent command into their system’s terminal. Nonetheless, this command initiates a series of occasions that results in the downloading/execution of additional malicious scripts, that are strategically hosted on a SharePoint website, in all probability to obscure the malicious operation inside a trusted cloud setting.
The preliminary PowerShell script performs checks to evade sandbox detection after which proceeds to obtain/execute a Python script, additionally hosted on SharePoint. This Python script acts as a shellcode loader and injects and executes a malicious DLL, KaynLdr, which reflectively masses an embedded DLL, and additional complicates evaluation through the use of API hashing.
The core of the attacker’s C2 infrastructure depends on the modified model of the Havoc Demon DLL because it leverages the Microsoft Graph API to determine communication channels that mix seamlessly with authentic cloud visitors. The “SharePointC2Init” perform inside the DLL obtains entry tokens for the Microsoft Graph API and creates two information inside the sufferer’s SharePoint doc library, every named with a singular identifier derived from the compromised system.
These information act as channels for transmitting sufferer data and receiving C2 instructions, whereas the whole communication is dealt with by the modified “TransportSend” perform and encrypted utilizing AES-256 in CTR mode. The agent then parses and executes these instructions, which embody a variety of post-exploitation capabilities, reminiscent of data gathering, file operations, and token manipulation.
FortiGuard Labs’s discovery highlights the evolution of open-source C2 frameworks to create new, difficult-to-detect assaults and the rising want for adopting superior safety measures towards such assaults.
“Along with staying alert for phishing emails, guided messages that encourage opening a terminal or PowerShell should be dealt with with further warning to forestall inadvertently downloading and executing malicious instructions,” FortiGuard’s researchers concluded.
In a remark to Hackread.com, Thomas Richards, Principal Advisor and Community and Crimson Crew Observe Director at Black Duck, a Burlington, Massachusetts-based software safety supplier, famous that hackers are utilizing trusted Microsoft providers to evade detection, exhibiting a excessive degree of sophistication, however what stands out is that their assault technique requires extra guide motion from the sufferer than common.
“These dangerous actor teams purpose for obfuscation to allow them to obtain their objectives. It’s common to see them use open-source frameworks, nonetheless, using authentic Microsoft providers reveals a degree of sophistication that’s regarding. Utilizing these providers permits them to cover in plain sight and have the advantages of being trusted servers,“ Thomas defined. “What’s shocking about that is the extent of guide intervention wanted on the sufferer for the assault to be successful. Normally with these campaigns, the dangerous actors need as little interplay as doable on the sufferer’s half except for clicking on a hyperlink.“