A large assortment of compromised information, dubbed “ALIEN TXTBASE,” has been built-in into the Have I Been Pwned, (an internet site that alerts customers about information breaches) database.
In accordance with Have I Been Pwned’s founder Troy Hunt, this data was harvested from people whose gadgets have been contaminated with infostealer malware designed to steal private information. This addition contains 1.5 terabytes of stolen credentials, containing 23 billion entries.
Evaluation of this information reveals 493 million distinctive e-mail and web site combos, impacting 284 million particular person e-mail addresses. Moreover, 244 million beforehand unknown passwords have been added to the Pwned Passwords database, with up to date frequency counts for an additional 199 million current entries.
Along with increasing the database, HIBP has launched new APIs to boost information accessibility for organizations. These APIs permit querying of stealer logs by e-mail and web site area, enabling assessments of workforce publicity and figuring out compromised buyer credentials. These instruments can be found by a Pwned 5 subscription, which incorporates an API for e-mail search and a free internet UI for e-mail log viewing. A brand new “IsStealerLog” flag is added for differentiated dealing with of stealer log information.
“Which means anybody programmatically coping with information in HIBP can now simply elect to deal with stealer logs otherwise than different breaches,” Hunt explained.
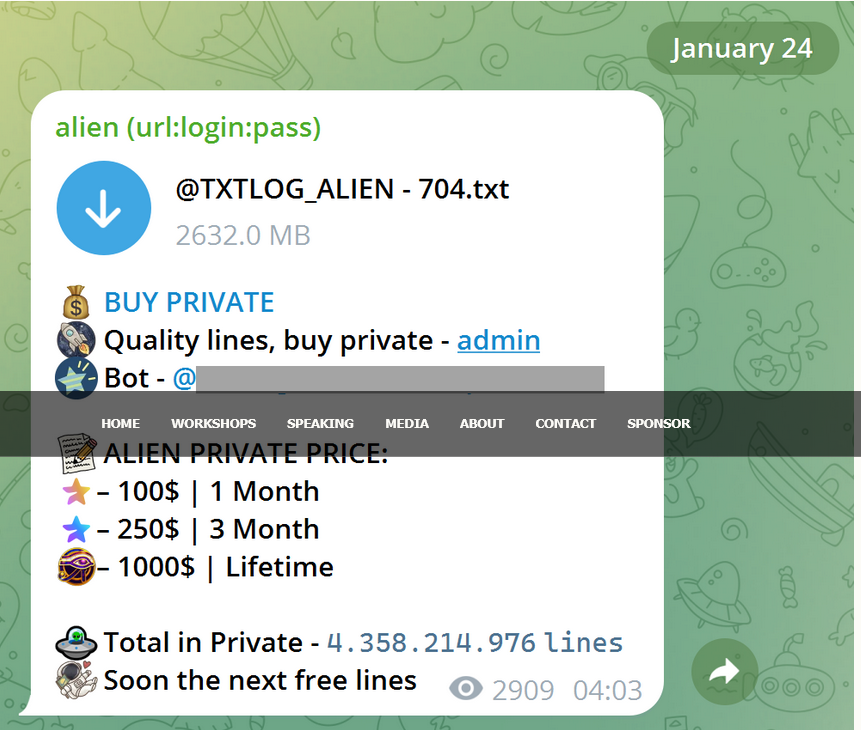
The ALIEN TXTBASE information originated from a Telegram channel distributing stolen credentials. This channel, one among many concerned in such actions, got here to gentle after a authorities company alerted HIBP to its existence.
“The file within the picture above contained over 36 million rows of knowledge consisting of web site URLs and the e-mail addresses and passwords entered into them.”
The info is disseminated in particular person information, a pattern of which reveals the channel’s monetization technique: providing free samples after which promoting subscriptions for entry to newly acquired stolen information. These credentials are usually obtained by malware infections, typically unfold by way of pirated software program or disguised inside seemingly respectable downloads. As soon as a machine is compromised, the malware silently harvests person credentials as they’re entered into web sites, enabling additional exploitation.
Not like breaches from single sources like a particular web site, the ALIEN TXTBASE breach concerned credentials from a mess of web sites, making it difficult to confirm their authenticity, Hunt famous.
Customary verification strategies like password resets are sophisticated by geo-fencing applied by some providers, similar to Netflix’s geo-restrictions. HIBP makes use of VPNs to confirm compromised accounts, and direct contact with its subscribers helped validate information. Whereas the info is essentially respectable, it might include fabricated entries, making it troublesome to differentiate legitimate from invalid data.
The ALIEN TXTBASE stealer logs are actually accessible by current HIBP search strategies, together with the newly launched domain-based APIs. This information empowers organizations and people to establish compromised credentials and take proactive steps to guard themselves. HIBP emphasizes that the free internet UI for viewing stealer log outcomes by e-mail stays out there. Customers can entry this function by visiting the notification web page and verifying their e-mail deal with.