FortiGuard Labs discovers Winos 4.0 malware concentrating on Taiwan through phishing. Learn the way this superior risk steals information and the way to shield your Home windows system.
Fortinet’s FortiGuard Labs has disclosed particulars of a brand new malware marketing campaign concentrating on Taiwanese companies. Reaching out to Hackread.com on this discovery, previous to its publishing on Thursday, researchers revealed that this marketing campaign was found in January 2025 and deployed a extremely superior malware framework, generally known as Winos 4.0. This assault exhibited a excessive severity degree, and utilized a multi-stage infection process, in the end aiming to steal delicate data for future malicious actions.
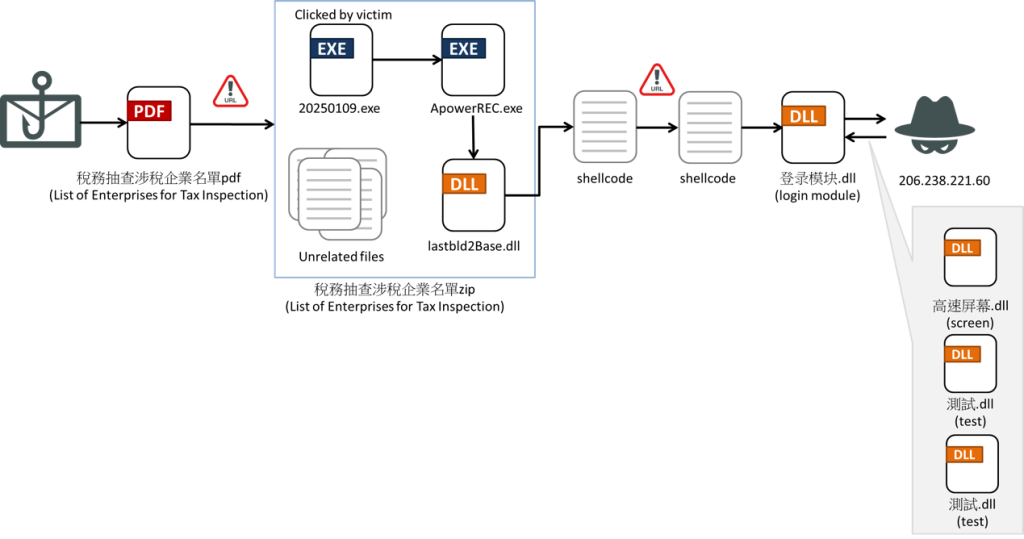
Additional probing revealed that this malware particularly focused Microsoft Home windows platforms. A phishing electronic mail, fastidiously crafted to impersonate Taiwan’s Nationwide Taxation Bureau, served because the preliminary assault vector. This misleading electronic mail claimed to comprise an inventory of firms scheduled for tax inspections, urging recipients to ahead the knowledge to their monetary departments. The connected file, disguised as an official doc from the Ministry of Finance, contained a malicious DLL for the following assault stage.
The assault unfolded by way of a collection of executable and dynamic hyperlink library (DLL) recordsdata. The ZIP file contained recordsdata that executed in a sequence: 20250109.exe, ApowerREC.exe, and lastbld2Base.dll.
“20250109.exe is a launcher initially used to execute the precise APowerREC.exe in ./app/ProgramFiles. The attacker created the identical folder construction within the ZIP file and used a loader to exchange ApowerREC.exe. The pretend ApowerREC.exe does nothing however name a perform imported from lastbld2Base.dll,” researchers defined within the blog post.
This DLL decrypts and executes shellcode, which comprises configuration information together with the command-and-control (C2) server handle. The shellcode additional implements non-compulsory options, similar to permission escalation, anti-sandbox methods (e.g. taking a number of screenshots to detect consumer exercise, delaying execution if no consumer interplay was detected), and course of window hiding. The malware downloads encrypted shellcode and the core Winos 4.0 module from the C2 server. This information was saved throughout the system’s registry for later decryption and execution.
The module initiates a number of malicious duties, similar to establishing persistence, bypassing UAC (Person Account Management), amassing system data (together with pc identify, working system model, and putting in antivirus software program), and disabling display savers and power-saving options on the contaminated system.
As well as, the malware actively screens and manipulates consumer exercise. This contains capturing screenshots, logging keystrokes and clipboard contents (even related USB units with their insertion and removing logs), and modifying clipboard information based mostly on predefined guidelines. It will probably additionally disable community connections for safety software program. Different assault chains had been additionally noticed, involving Python scripts and additional shellcode injection methods. These variations reveal the flexibleness and adaptableness of the Winos 4.0 framework.
Defending your self from subtle malware like Winos 4.0 requires being extremely suspicious of unsolicited emails, particularly these with attachments or hyperlinks, avoiding opening compressed recordsdata (ZIP, RAR) connected to emails, as they’re typically used to ship malware, and enabling real-time scanning to detect and block threats earlier than they’ll infect your system.
Consultants Feedback
“This assault follows a traditional phishing sample however with a enjoyable twist across the trusted authority to invoke a response,” explains J. Stephen Kowski, Discipline CTO at SlashNext. “The risk actors cleverly exploit human psychology by creating urgency and curiosity, making recipients extra more likely to obtain malicious content material.”
Past electronic mail safety, Kowski highlights the significance of a multi-layered strategy to defence. “Most organizations at the moment are utilizing managed file switch programs that require registration and inner approval whereas concurrently blocking zip attachments altogether. Combining consumer schooling with superior risk detection applied sciences is essential to stopping subtle social engineering makes an attempt earlier than they attain inboxes.”