
Twitter (X) Hit by Data Leak of 2.8 Billion Users; Allegedly an Insider Job
A knowledge leak involving a whopping 2.87 billion Twitter (X) customers has surfaced on the notorious Breach Boards. In response…

A knowledge leak involving a whopping 2.87 billion Twitter (X) customers has surfaced on the notorious Breach Boards. In response…

An information leak involving a whopping 2.87 billion Twitter (X) customers has surfaced on the notorious Breach Boards. In response…

Cryptocurrency can be extra fashionable in 2025 than it has ever been and this implies that there’s a higher want…

Internet Software Penetration Testing (WAPT) is a methodical strategy to safety that entails moral hackers simulating real-world cyber-attacks in your…

Mar 29, 2025Ravie LakshmananRisk Intelligence / Cell Safety Cybersecurity researchers have found a brand new Android banking malware referred to…

Palo Alto, USA, March twenty eighth, 2025, CyberNewsWire From WannaCry to the MGM Resorts Hack, ransomware stays one of the…

Mar 29, 2025Ravie LakshmananCybercrime / Vulnerability In what’s an occasion of hacking the hackers, risk hunters have managed to infiltrate…
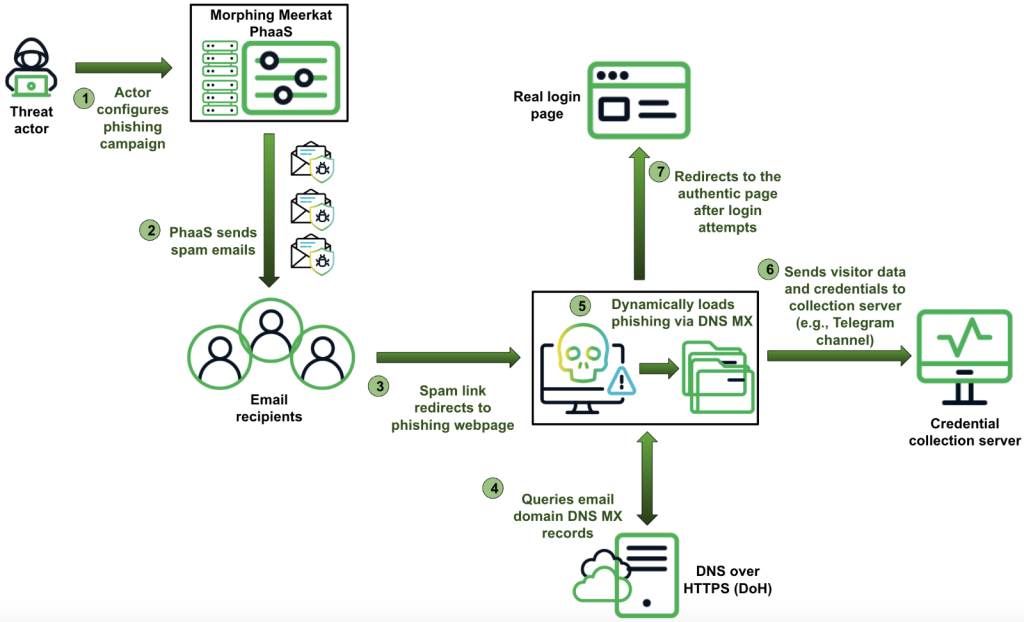
A latest evaluation revealed by Infoblox reveals a classy phishing operation, dubbed Morphing Meerkat, actively exploiting DNS vulnerabilities for years…
Let’s face it: Rolling out new software program throughout a complete group can really feel like herding cats. Between knowledge…

Whereas inundated with concepts, you additionally want to think about the right way to current them successfully and construction the…